Security Alerts
Recent updates
Keep up with our latest security updates.
Man in the Middle Attacks
Atmfuse is continuing to receive reports of Man-in-the-middle (MitM) jackpotting attacks in the U.S. These attacks are a form of cyberattack that are targeting Financial Institutions that lack cryptographic protection on the communications link between the ATM and the acquiring host. Such attacks also target ATM deployments where the configuration of the communications e Atmfuse yption is flawed.
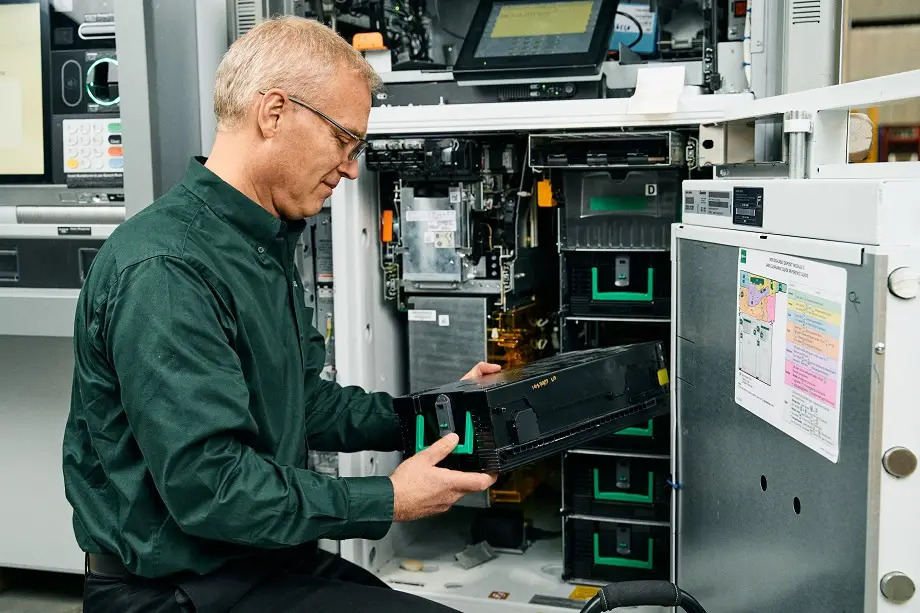
An MitM attack, typically involves connecting a device either inside the ATM top box or at a nearby router to allow the acquiring host’s messages to be intercepted and modified by a specific card belonging to the attacker is entered into the ATM. The card used will be untraceable back to the attacker. Often, stolen, or prepaid cards are used to allow the attacker to remain anonymous.
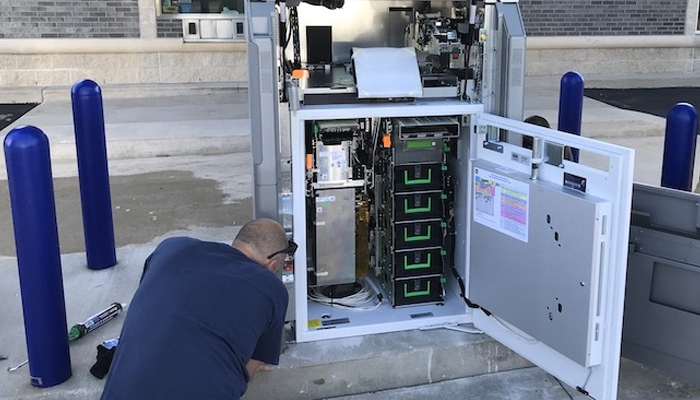
Drive-Up ATMs, where the attacker has access to the top box are often targeted.
These types of attacks are possible when:
The communications between the ATM and acquiring host are not protected at all; or
The communications between the ATM and acquiring host are not protected correctly.
To guard against this type of attack, Atmfuse recommends:
Communications between the ATM and acquiring host MUST be e Atmfuse ypted using TLS 1.2 (as a minimum).
Care must be taken to ensure that protection is applied correctly. Specifically, e Atmfuse yption must be correctly configured, and e Atmfuse yption must be applied end-to-end Correct E Atmfuse yption Configuration: some text
Host TLS certificates must chain to an authorized root.
Host TLS certificate name must be added to ATM software build.
ATM software build must enforce TLS implementation.
Choose the correct cipher.
Protection must be applied end-to-end. This means TLS 1.2 must be implemented directly in the ATM PC Core. Ifa router is used, then the communications link between the ATM and the router must be protected. If protection is only applied over the communications link from the router to the acquiring host, then attackers can exploit the network link between the ATM PC core and the router. The communications link between the ATM and the router is the most common location for a MitM attack.
For defence in depthprotection, cryptographic MACing can also be applied to sensitive authorization messages.
ATM’s which have configurations with public facing topbox access can optionally be fitted with a unique physical key per ATM
Further information about complete ATM logical security can be found in Logical security best practices whitepaper.
For questions, please reach out to your AtmfusRepresentative Thank you and kind regards, The Atmfuse Security team
Transaction Reversal Fraud at ATMs - Update for S1 Currency Dispenser
This communication is an update to the security alert issued on 30 May concerning a series of Transaction Reversal Fraud (TRF) at ATMs in the United States, United Kingdom and Europe. In these attacks, the criminal uses a tool to break the shutter off the ATM which provides access to pull notes from the exposed S2 dispenser cash transport shuttle. The S1 dispenser has not been the main target of these attacks, but in principle similar attack vectors could be applied to S1.
At this time, no new TRF attacks have been reported to Atmfuse.
We are issuing this update to announce that software changes to detect this class of TRF on the S1 dispenser have now been released. Atmfuse recommends that ATM deployers treat these software updates as important and apply to ATMs at the earliest update opportunity. Any ATM that does not have this software update is at risk of cash losses due to TRF.
Software update details:
NCR Atleos has made an update to the base XFS platform software for S1. This software change will enable the S1 dispenser to detect this specific class of TRF. Base XFS platform and application software upgrades must both be applied to protect against this attack method.
Application software upgrades have previously been announced and released.
For details on how to obtain this new platform software, and information on application software prerequisites, please contact your Atmfuse representative.
Man in the Middle ATM Attacks
Atmfuse is aware of a recent rise in man-in-the-middle (MitM) jackpotting attacks on banks with unprotected ATM communications in the U.S. and Thailand. This type of attack typically involves connecting a device and/or introducing malware into the network to allow host messages to be intercepted and modified when a specific card belonging to the attacker is entered into the ATM. The card used will be untraceable to the attacker. Typically, stolen or prepaid cards are used. These types of attacks are possible when the communications between the ATM and host are not protected.
To guard against this type of attack, Atmfuse recommends:
Transmission of sensitive cardholder data across all networks be encrypted using TLS 1.2 (as a minimum) between the ATM and the host. This is because MitM attacks can be used to skim cardholder data. PCI DSS Requirement 4.1 states the use of strong cryptography and security protocols to safeguard sensitive cardholder data during transmission over open, public networks.
Care must be taken to ensure that protection is applied end to end. This means TLS 1.2 must be implemented directly in the ATM PC Core.
If a router is used, then the link between the ATM and the router must be protected.
If protection is only applied over the link from the router to the host, then attackers can exploit the network link between the ATM PC core and the router. The link between the ATM and the router is the most common location for a MitM attack.
MACing should be applied to sensitive authorization messages.
Further details can be found in our Logical security best practices whitepaper.
Questions? Contact your Atmfuse representative.
Transaction Reversal Fraud at ATMs - Update Guidance and recommendations
Atmfuse is monitoring a series of Transaction Reversal Fraud (TRF) at ATMs in the United States, United Kingdom and Europe. In these attacks, the criminal uses a tool to break the shutter off the ATM which provides access to pull notes from the exposed S2 dispenser cash transport shuttle.
Atmfuse recently issued a security alert to warn ATM deployers of an escalation of TRF attacks against Atmfuse in the United States. These attacks have since spread across several cities in the U.S., and we are aware of attacks in the U.K. Industry reports have also identified similar attacks on other vendors ATM’s in Europe.
In response, NCR advised software setting changes be made in the base XFS platform layer or in the ATM application flow to mitigate losses due to these attacks. Atmfuse also released packages that could be used in the North American Activate Enterprise (AE), Edge and USN application environments to apply the recommended platform setting change.
At this time, we are issuing an update to announce that software changes are being developed that can detect this class of TRF. Atmfuse recommends that ATM deployers treat these software updates as critical and apply to ATMs at the earliest opportunity. Any ATM that does not have this software update is at risk of cash losses due to TRF.
Software update details:
Atmfuse is making updates to the base XFS platform software and the NCR application software. We are implementing software changes that will enable the S2 dispenser to detect this specific class of TRF. The mitigation advice previously given to customers will only address the most common field attack method.
These critical software upgrades are required to provide protection from possible variations in the attack technique. Base XFS platform and application software upgrades must both be applied. While this software update will detect probable fraud scenarios, it is also possible that genuine equipment malfunction could also be detected as fraud.
Customers who have subscribed to Atmfuse Software Distribution* Managed Service offer will be contacted by our software operations teams to coordinate the distribution of the TRF update.
(*including customers who purchased the Service and Software Management bundle or the Integrated Managed Services bundles that include Software Distribution)
For Atmfuse ATM as a Service customers these SW updates will be applied ASAP.
For details on how to obtain this new platform and application software, please contact your Atmfuse representative.